As you are probably aware Microsoft has been removing basic authentication capabilities in Office 365 services, which includes connectivity using ‘legacy’ protocols like IMAP, POP or SMTP.
While this removal is for the greater of good – basic authentication is not a secure way to authenticate as it can be easily hack and does not support multi-factor authentication (MFA), which is helping securing identity – this also has a downside.
Indeed, companies may still rely on these legacy protocols which support only basic authentication due to legacy applications or multi-function printers.
Well good news as you can now use OAuth authentication (to know more about OAuth you can read this article https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-v2-protocols; OAuth implementation on Microsoft services relies on the use of the Microsoft Authentication Libraries (MSAL) where you can learn about here https://docs.microsoft.com/en-us/azure/active-directory/develop/msal-overview) – a more modern authentication method which also support MFA – when connecting with any of these legacy protocols – IMAP, POP or SMTP – to Exchange Online.
To do so you will need to register an Azure AD application which then will get an access token and then authenticate the connection request using this token.
Here are the steps to implement OAuth authentication for the legacy protocols.
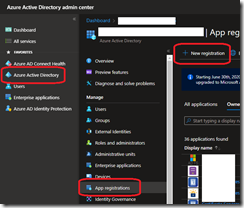
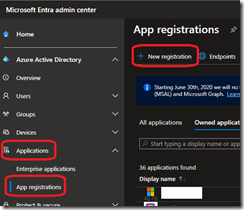
First logon to your Azure AD portal (https://aad.portal.azure.com/) to access the Azure Active Directory\App Registrations blade or even better start using the new Entra portal (https://entra.microsoft.com/) to access the Azure Active Directory\Applications\App registrations blade.
To do so you need to have either Global administrator, Application administrator, Application developer or Cloud application administrator administration role.
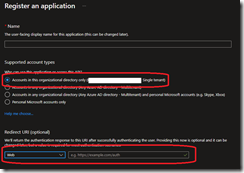
When registering the Azure AD application you just need to ensure you choose an understandable name and the supported account types set to Accounts in this organizational directory only; the redirect URL is not important can be set to any HTTPS value
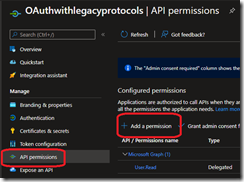
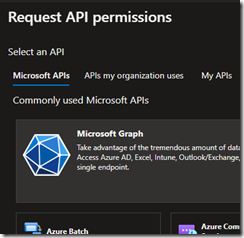
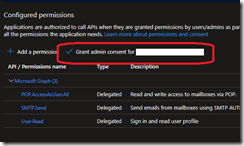
Then you will need to grant the appropriate Microsoft Graph\Delegated Permissions permissions (IMAP.AccessAsUser.All, SMTP.Send, or POP.AccessAsUser.All) using the API permissions blade; select the API permissions based on the protocol(s) you are planning to use
Once you have added the required permissions you have to grant them using the Grant admin consent for <your tenant name>
Now your Azure AD application is created with the permissions to connect to Exchange Online using the configured legacy protocols.
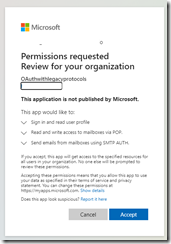
You will now need to grant tenant admin consent to this application using the below URL; you need to replace the <tenant> parameter with your Azure AD directory ID, <CLIENT_ID> with the Azure AD Application ID and the <REDIRECT_URI> to the redirect URI of your application
https://login.microsoftonline.com/{tenant}/v2.0/adminconsent?client_id=<CLIENT_ID>&redirect_uri=<REDIRECT_URI>&scope=https://ps.outlook.com/.default
Depending on or your redirect URL you may have an HTTP error; this is not important as this is just because your browser is not able to resolve the redirect URI. It is all fine.
Now as the last steps you need to register your Azure AD Application service principals in Exchange Online and grant access to the Exchange Online mailbox to this service principal.
To do you will need to have either Exchange Online administrator or Global administrator administration role and use the Exchange Online PowerShell module V2 (available here https://www.powershellgallery.com/packages/ExchangeOnlineManagement/2.0.5).
The <APPLICATION_ID> and <OBJECT_ID> are the corresponding values for your Azure AD application wile the <ORGANIZATION_ID> is the Directory ID.
NOTE the New-ServicePrincipal and/or the Get-ServicePrincipal cmdlets are currently being deployed and may not be available yet in your tenant
Connect-ExchangeOnline
New-ServicePrincipal -AppId <APPLICATION_ID> -ServiceId <OBJECT_ID> [-Organization <ORGANIZATION_ID>]
Get-ServicePrincipal -Organization <ORGANIZATION_ID>
Add-MailboxPermission –Identity <mailbox identity> -User <SERVICE_PRINCIPAL_ID> -AccessRights FullAccess






Hi, could you please explain how can I find the New-ServicePrincipal cmdlet? I did not find it in any of the installable module about exchange, nor it works connecting to three office365 account, I just don’t get how to find that cmdlet.
This is not an Exchange Online PowerShell but an Azure PowerShell (see https://docs.microsoft.com/en-us/powershell/azure/create-azure-service-principal-azureps?view=azps-8.2.0&WT.mc_id=M365-MVP-7836)