As you should already know you can use Azure Key Vault to store secret (either keys, secret or certificates) in a secure way for use by end users and/or automation.
Well, until then when you had a key going to expired you had to manually renew/update it.
Not anymore, you can now configure auto-rotation to automatically create a new key version when needed.
Before you start looking into it, few things:
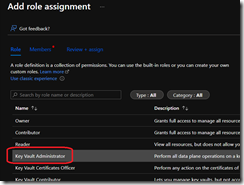
- You need to have Key Vault Administrator role assigned to the user/group going to manage the auto-rotation feature
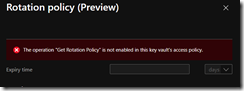
- You need to grant the Rotation and Get Rotation Policy permissions in the Access Policies
- You can enable the auto-rotation on existing keys
During the preview there is no cost associated with it; once GA, there will be a cost (US $1 per rotation).
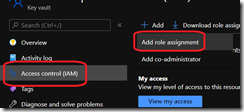
Grant the Key Vault Administrator role
Connect to your Azure portal (https://portal.azure.com) to access the Access Control blade of the Key Vault you want to grant the role and configure auto-rotation
Enable the Rotation permissions
To enable the Rotation permissions, access the Access Policies to edit existing policy or create a new one and grant at minimum the Get Rotation Policy permission; you can also grant the Rotate permission if you want to allow the identity to allow the rotation on demand
If you don’t grant these permissions, when you will create a new Key and configure the the auto-rotation you will get the error
The operation “Get Rotation Policy” is not enabled in this key vault’s access policy.
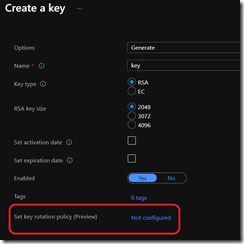
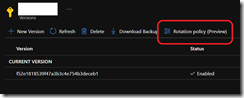
Configure the auto-rotation
You can enable the auto-rotation during the creation of a new key or edit an existing one by accessing the key and access the Rotation policy tab
The Expiry time must be at least 28 days
If you also have granted the Rotate permission to the identity, you can use the Rotate now to immediately rotate the version; this can be helpful if you urgently need to rotate