It has been in preview for the past few months, it is now GA (generally available): you can now invite external users (Azure AD B2B – Business to Business) using Google ID as identity provider, supporting @gmail.com and @googlemail.com email address domains.
Before enabling support for Google ID, you first need to create a Google client ID and secret by accessing https://console.developers.google.com/; it is recommended to use a shared Google account to logon
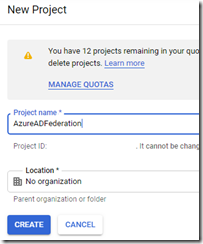
Create a new project and name it; optionally if you already have an organization configured you can also define it
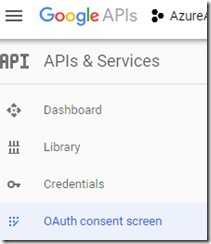
Once your Google API project has been created, configure the OAuth consent screen option of your project
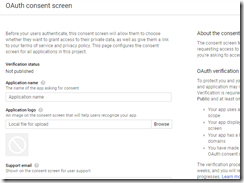
There define the application details and define the Authorized domains with the value microsoftonline.com
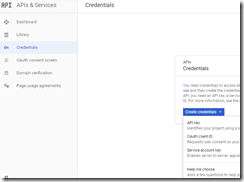
Once done, save it and access the Credentials option to create an OAuth client ID
Select Web application and define the settings with Authorized redirect URIs set to:
- https://login.microsoftonline.com
- https://login.microsoftonline.com/te/<directory id>/oauth2/authresp
(where <directory id> is your directory ID)
Save the client ID and secret.
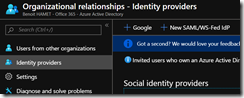
Then you can logon to your Azure portal (https://portal.azure.com/) or Azure AD Portal (https://aad.portal.azure.com/) to enable Google ID federation for your Azure AD and reach the Organizational relationship
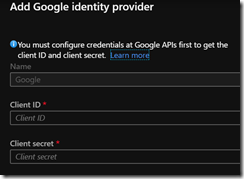
Then access the Identity Providers to add the Google one on which you define the client ID and secret you have created above
You can also enable it using PowerShell using the below command
New-AzureADMSIdentityProvider -Type Google -Name Google -ClientId [Client ID] -ClientSecret [Client secret]
That’s it, you are now federating with Google identity services. You can now invite external/guest users using their Google account.