You can now associate up to 100 public IP with your Azure Firewall.
This allows you to implement more NAT scenario – Source NAT (SNAT) and/or Destination NAT (DNAT).
A DNAT scenario will be translating the same communication port (let say TCP 443 for example) while targeting different internal host.
A SNAT scenario will allows you to randomly use a different public IP when accessing external networks, like Internet.
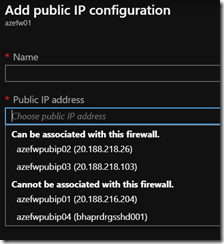
To be able to be associated with your Azure Firewall, the public IP must use the Standard SKU.
Then you can use either Azure portal, Azure PowerShell, Azure Cli or REST to manage public IP for your firewall.
NOTE it is important to note that you can not delete the first public IP associated with your Azure Firewall
The below steps assume you already have created your additional public IP using the Standard SKU.
Using the portal
You can not add multiple public IP during the firewall creation when using the portal.
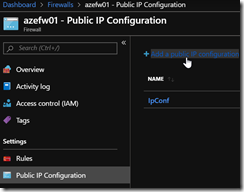
Connect to your Azure portal (https://portal.azure.com) and reach out the Firewall configuration blade
Edit the Azure Firewall you want to associate additional public IP by accessing the Public IP Configuration blade and Add a public IP configuration
Then select the public IP you want to associated with your firewall; you can notice the drop down list shows you which IP’s can be or can’t be associated with the firewall
Using PowerShell
You use either the Cloud Shell or the Az module you have installed locally (as always, it is recommended to ensure you use the latest version – 2.5.0 at the time of writing this post)
Create a firewall with multiple public IP
$pip1 = Get-AzPublicIpAddress –Name <name of your first public IP> -ResourceGroupName <your resource group name>
$pip2 = Get-AzPublicIpAddress –Name <name of your second public IP> -ResourceGroupName <your resource group name>
New-AzFirewall -Name “<name of your firewall” -ResourceGroupName <your resource group name> –Location <location of the firewall> –VirtualNetwork <your virtual network> -PublicIpAddress @($pip1, $pip2)
Add a public IP to an existing firewall
$pip1 = Get-AzPublicIpAddress –Name <name of your public IP> -ResourceGroupName <your resource group name>
$azFw = Get-AzFirewall -Name “<name of your firewall” -ResourceGroupName <your resource group name>
$azFw.AddPublicIpAddress($pip1) $azFw | Set-AzFirewall