As you may already know, Microsoft has proposed to secure access to your cloud (as well as you on-premises) application using MFA (Multi Factor Authentication) based on Azure MFA (formerly Phone Factor) – see http://blog.hametbenoit.info/2014/08/18/azure-use-windows-azure-multi-factor-authentication-to-secure-your-on-premises-application-and-with-your-adfs/ (on-premises MFA) and http://blog.hametbenoit.info/2013/10/11/office-365-setup-multi-factor-authentication/ or http://blog.hametbenoit.info/2013/06/17/office-365-manage-multiple-factors-authentication/ for Office 365 and cloud apps for more details.
But, until then, as soon as a user has been setup to use MFA, this applies to ALL application he is trying to access.
Now, this will be possible to setup per-application MFA requirement (currently in preview). This means a user (enabled for MFA off course) will be able to access application and depending of the application may be requested to enter his MFA to continue the authentication process.
Configure per-application MFA
Off course, you must have enabled MFA for your Azure / Office 365 tenant before being able to setup this.
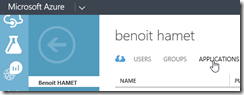
Then, from the Azure management portal (https://manage.windowsazure.com) logon using an administrator account and reach the Active Directory section, select your directory and open the Applications tab
Add a federated application (or hit an existing federated app to reach his settings) and configure his single sign on setting and ensure/choose Windows Azure AD Sign-On option; if you are adding a new application you may have to define the sign in URL
Then, hit the Configure tab for the application – NOTE not all application may have this tab available
Then reach out the Access Management section and switch from All users to Groups the Apply to settings
Then you can select the group(s) which will require MFA to access the application.
You can also add exception to exclude some users which are part of the selected group(s).
Next time the user will logon to the application, he will be requested to use MFA only if he is member of the group(s) selected here.