![]() As you know, certificates are now widely used from securing network traffic (HTTPS) to authentication (certificate based authentication, VPN or WiFi authentication).
As you know, certificates are now widely used from securing network traffic (HTTPS) to authentication (certificate based authentication, VPN or WiFi authentication).
Until now, if you wanted to use certificates for authenticating devices or users, you had to deploy and use your own certificate authority, usually requiring an Active Directory domain and multiple servers to host the root and subordinate authority servers and additional servers to deliver related services – such as NDES, usually on-premises or running on virtual machines hosted in the cloud.
With the move to cloud services, the need for cloud public key infrastructure (PKI) to deliver certificates has been growing.
Well, good news, after a long awaited move from Microsoft, you can now use a Cloud PKI capability with your Intune services.
To take advantage of this, you need either:
- Intune Suite license – available now
or
- the Cloud PKI add-on – available in March
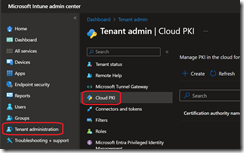
Once you have the appropriate licenses, you can start implementing your Cloud PKI by accessing the Tenant administration\Cloud PKI blade from the Intune portal (https://intune.microsoft.com/).
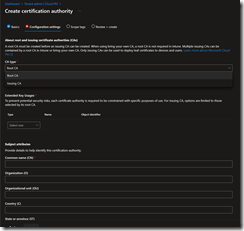
You first have to create a root certificate authority (same as for on-premises) and select the certificate usage before creating an issuing authority (similar to the subordinate on-premises one).
If you have already an on-premises you can discard the root CA creation step and go straight to create the issuing authority.
The various settings are using the same values than for on-premises, for example Country value will be the corresponding country code.
Same as for on-premises certification authority, you can’t edit the properties once the authority is created.
Once the root CA is created you can access it to download the certification authority certificate; this will be need for trusting certificates generated by the issuing authority.
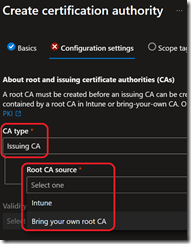
Once the root CA is created, you can now create the issuing authority. Repeat the steps above but select the Issuing CA type and the root you want to use – either the one your just created (Intune) or import your on-premises CA certificate.
Import of the existing CA certificate will be possible once the issuing CA has been created
Once the issuing CA is created, access it to download the certificate and grab the SCEP URI; the URI will be needed when configuring the NDES service
The next steps are to create the corresponding Intune device configuration profiles to deploy the CA certificates and the SCEP service (this is when you will use the SCEP URI from the previous step).
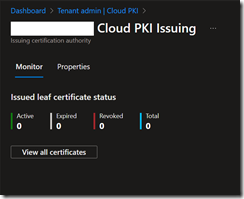
You can monitor certificates status from the Monitor tab of the issuing authority.
From there you can also have the list of all certificates.