Azure Firewall can now learn address ranges and automatically configure them to be excluded from Source Network Address Translation (SNAT) for outbound connections (see https://learn.microsoft.com/en-us/azure/load-balancer/load-balancer-outbound-connections/).
This helps reducing time and complexity when manually defining SNAT ranges.
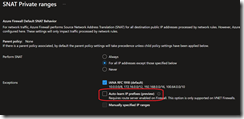
When auto-learn SNAT functionality, the auto-learn will configure the firewall every 30 minutes for both registered and private ranges.
These learned address ranges are considered to be internal to the network, so traffic to destinations in the learned ranges aren’t SNATed.
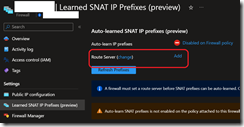
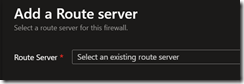
Auto-learn SNAT ranges requires Azure Route Server to be deployed in the same VNet as the Azure Firewall.
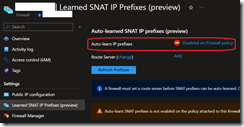
The auto-learn SNAT is enabled within the Azure firewall policy.
Before enabling this new functionality, you need to add a new subnet to the existing firewall vNET:
- Subnet name: RouteServerSubnet
- Subnet size: at least /27
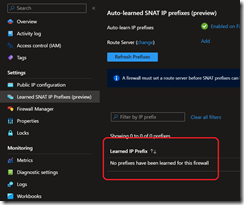
Then search for the firewall you want to enable auto-learn SNAT to edit the policy from the Learned SNAT IP Prefixes blade
and then set the route server
Once enabled, you can then see the learned prefixes in the same blade under the Learned IP Prefixes section