The release of System Center Configuration Manager Current Branch 1906 (SCCM Current Branch) is providing an updated discovery method to your Azure AD tenant.
As you may be already aware, you have been able to discover your Azure AD users objects with SCCM for quite some time now.
Well, this Azure AD discovery functionality has been updated with SCCM 1906 to also allow you to discover your Azure AD Security Group.
To enable this new discovery, open your SCCM administration console and reach out the Administration\Cloud Services\Azure Services workspace and edit your Cloud Management configuration
Then reach the Discovery tab and enable the Azure Directory Group Discovery
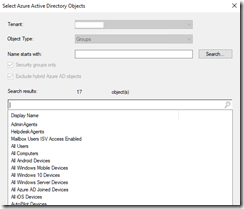
When enabling this discovery method you also have to define a scope by edit the Settings; defining a scope will ask you to authenticate against your Azure AD when performing the search
If you don’t enable a scope, you will get an SMS provider error when running the full discovery
ConfigMgr Error Object:
instance of SMS_ExtendedStatus
{
Description = “Parameter DiscoveryScopeIds is null or has the wrong type”;
ErrorCode = 1078462208;
File = “..\\sspaaddiscoverysettings.cpp”;
Line = 198;
ObjectInfo = “DiscoveryScopeIds”;
Operation = “PutInstance”;
ParameterInfo = “”;
ProviderName = “ExtnProv”;
StatusCode = 2147749889;
};——————————-
Microsoft.ConfigurationManagement.ManagementProvider.WqlQueryEngine.WqlQueryException
The SMS Provider reported an error.Stack Trace:
at Microsoft.ConfigurationManagement.ManagementProvider.WqlQueryEngine.WqlResultObject.Put(ReportProgress progressReport)
at Microsoft.ConfigurationManagement.ManagementProvider.WqlQueryEngine.WqlResultObject.Put()
at Microsoft.ConfigurationManagement.AdminConsole.CloudServicesManagement.CloudManagementAction.RunFullDiscovery(Object sender, ScopeNode scopeNode, ActionDescription action, IResultObject selectedResultObject, PropertyDataUpdated dataUpdatedDelegate, Status status)——————————-
System.Management.ManagementException
Generic failureStack Trace:
at Microsoft.ConfigurationManagement.ManagementProvider.WqlQueryEngine.WqlResultObject.Put(ReportProgress progressReport)
at Microsoft.ConfigurationManagement.ManagementProvider.WqlQueryEngine.WqlResultObject.Put()
at Microsoft.ConfigurationManagement.AdminConsole.CloudServicesManagement.CloudManagementAction.RunFullDiscovery(Object sender, ScopeNode scopeNode, ActionDescription action, IResultObject selectedResultObject, PropertyDataUpdated dataUpdatedDelegate, Status status)——————————-
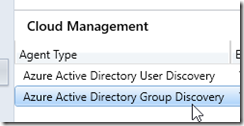
Once enabled you should see a new agent type called Azure Active Directory Group Discovery
You can monitor/troubleshoot the Azure Active Directory discovery methods using the SMS_AZUREAD_DISCOVERY_AGENT.log log file (shared with Azure AD User Discovery).
Below an example of a successful discovery in the log and then in the Assets and Compliance\Users workspace – the Domain column is empty Azure AD groups and you can see in the properties the Agent used (SMS_AZUREAD_USER_GROUP_DISCOVERY_AGENT) and the tenant ID and group ID from Azure AD.