You may already Azure Information Protection (AIP) is used to protect and classify your data.
You may aware you can also automated classification and protection for your data hosted online.
Now, you can use Azure Information Protection Scanner to automatically classify and protect your files hosted on-premises, either on file servers or SharePoint (2013 or 2016).
In a nutshell, we could say this is the replacement of the previous Azure RMS Connector.
The AIP Scanner can be used in 2 modes:
- discovery, to gather data and analyze the result
- automatic labeling, to automatically apply the classification and protection using Office 365 Data Loss Prevention (DLP)
AIP Scanner works for files which can be indexed by Windows using iFilter. You can get the list of these file types here https://docs.microsoft.com/en-us/information-protection/rms-client/client-admin-guide-file-types
Prerequisites
Before deploying the AIP Scanner, you need to ensure you have the following available:
- Windows Server 2012R2 or 2016 (for testing purpose you may deploy it on any AIP supported version of Windows)
- SQL Server 2012 (at least) – either Express, Standard or Enterprise edition – deployed either locally or remote
- The service account need to be granted the dbcreator and securityadmin SQL permissions
- A service account authorized to log on locally, log on as a service on the server running AIP Scanner and read/write permissions on the files to protect
- The setup process will grant the local permissions to the account
- Azure Information Protection classification and label – if you want to automatically protect your files
Recommendation it is recommended to make the service account a super user for Azure Information Protection (making it mandatory to be synced with Azure AD) (see https://docs.microsoft.com/en-us/information-protection/deploy-use/configure-super-users to manage AIP super users)
- Download the setup file from https://www.microsoft.com/en-us/download/details.aspx?id=53018. NOTE currently this is a separate download (AzInfoProtectionScanner.exe). Future release will be included in the AIP client.
Azure Applications Creation
2 applications need to be created on Azure AD to get AIP Scanner running in an unattended mode – aka being able to authenticate against your AIP.
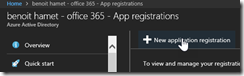
- Logon to you Azure AD portal and access the App Registrations blade for your Azure AD
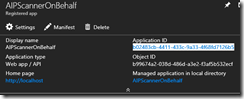
- Create a new web app/API application
- Name it as you wish (as usual use a name which means something), set the application to type to Web app/API (default) and the sign-on URL to http://localhost
- Get the Application ID of the newly created application by accessing the properties
- Apply the appropriate permission by accessing the Settings and then Required Permissions and click to the Grant permissions button
- Create a key which will be used to authenticate against this application by accessing the Settings\Keys blade. Name the key (as you wish) and define the expiration period. Recommendation do not set it to never expires
IMPORTANT Take note of the value when you click Save, once saved you will not be able to get again this value
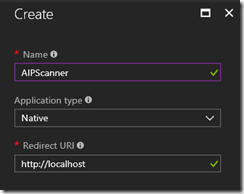
- Create another application, using the Native type and set the redirect URL to http;//localhost
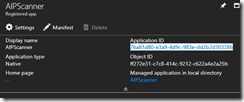
- Access the settings of the newly created native application to gather the application ID
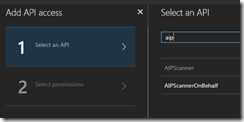
- Then access the Settings\Permissions blade to grant the permission for the web app application created previously
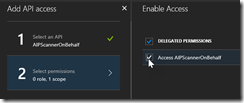
- Search for the web app application and enable the access
- Apply the appropriate permission by accessing the Settings and then Required Permissions and click to the Grant permissions button
- Apply the appropriate permission by accessing the Settings and then Required Permissions and click to the Grant permissions button
Install and configuration
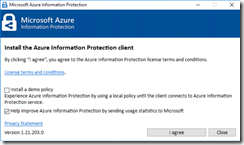
- Run the AzInfoProtectionScanner.exe file to install AIP Scanner
NOTE after the setup is completed, you will notice the AIP client (Azure Information Protection Viewer) has been installed
- Open a PowerShell prompt using the run as administrator option to run the PowerShell command to install the scanner
$cred = Get-Credential
Install-AIPScanner –SqlServerInstance <sqlserver when using a remote SQL server with default instance or sqlserver\instance when using a remote SQL server with named instance> –ServiceUserCredentials $cred
NOTE the service account must entered using the domain\user format
- Once completed, a database called AzInfoProtectionScanner is created on the SQL server and a service called Azure Information Protection Scanner (AIPScanner)
- Then run the following PowerShell command to complete the configuration; when running this command you will be prompted for authentication.
Set-AIPAuthentication -WebAppId <Azure web app application ID> -WebAppKey <web app application key> -NativeAppId <Azure native application ID>
NOTE when the web app application key expire, just renew it by creating a new one and re run the previous command with the updated values
You can now start the Azure Information Protection Scanner service
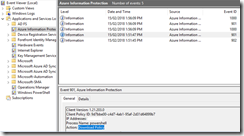
You can check on the local server the Azure Information Protection log for event 901 and 902 to confirm the scanner signed in and has downloaded the policy
You may also have a 1000 event ID logged; this means the scanner has stopped because no repositories are configured.
Last but not least, you need to add one or more location for AIP Scanner to scan and apply classification.
But first, it is recommended to run a discovery and analyze the result.
Add repository to scan
To add a repository to scan, run the command
Add-AIPScannerRepository -Path <path>
NOTE after adding the first repository you may have to start again the service has to be have been automatically shutdown
You can check the event log for event ID’s 910 and 911, showing respectively the start and the finish of the scan
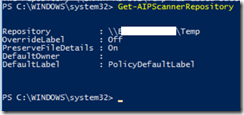
Get existing scanned repositories
Get the list of all repository using the command; you will get all the repositories being scanned with the default label policy being applied
Get-AIPScannerRepository
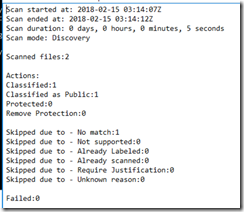
Scan Mode Configuration
AIP Scanner mode configuration is done using the command, associated with the below parameters (ScanMode and Schedule)
Set-AIPScannerConfiguration
- discovery mode: -ScanMode Discover
- classification enforcement mode: –ScanMode Enforce
- continuous scan: –Schedule Continuous
- one time scan: –Schedule OneTime
It is recommended to run first a discovery mode and to get the reports saved in%localappdata%\Microsoft\M
SIP\Scanner\Reports directory